There are several ways to raise business notifications in Azure Logic Apps. One way is to add an Office365 or SendGrid email action directly to the Logic App. Another is to call a common Logic App that handles sending emails to appropriate audiences. Perhaps another option is to send notification details to a Service Bus Queue or Topic that is subscribed by the common Logic App.
Each of these approaches have certain limitations:
- If using an email action directly in a Logic App then each Logic App must know the destination email address.
- An email action also makes it difficult to change how notifications are sent e.g., switch from Office365 to SendGrid, or add another destination like PagerDuty.
- Sending notification requests from your Logic Apps also means the decision to send a notification is baked into the Logic App. Changes to notification rules may mean changing many Logic Apps.
Leverage Log Analytics and Alert Rules
A better approach is to abstract away completely the sending of notifications from the source. Data that could potentially be used for a notification are written to Log Analytics. Alert Rules are created over these data that will trigger when a business notification should be sent. The Common Alert Schema supplied by the Alert Rule is used by a generic Logic App that sends business alerts.
This method solves the issues of the other approaches.
- The source Logic App does not need to know about how a business notification is sent or to whom.
- The source Logic App doesn’t even need to know that a notification needs be raised.
- The notification handler can be changed independently.
- Alert Rules contain the logic for raising notifications and can be changed independently from the source.
- The data written to Log Analytics may be used for more than just notifications.
This article describes how to use Azure Log Analytics to generate business notification emails from Logic Apps.
Log Analytics for Logic Apps the Easy Way
Log Analytics is ideal for raising business notifications. A simple method is to use a Log Analytics Custom Log monitored by an Alert that runs a Logic App responsible for formatting and sending an email to a business user. This method minimises the amount of data that are sent to Log Analytics.
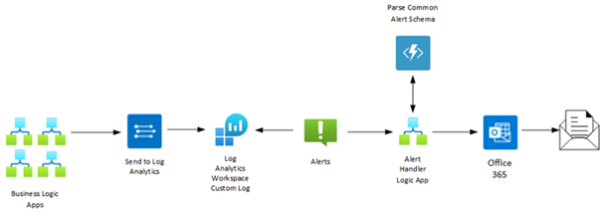
How It Works
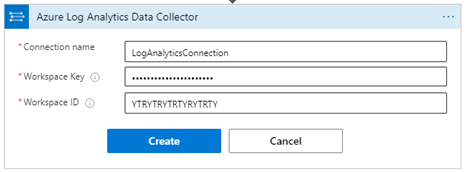
Any Logic App that needs to email a business user writes details to a Custom Log using the Azure Log Analytics Data Collector Send Data action:
This action sends name-value pairs to a custom log of your choice. If the custom log name does not exist, then it will be created automatically.
An Alert Rule that regularly queries the custom log is triggered and calls an Alert Handler Logic App passing an Azure Monitor Common Alert Schema message. This message contains a generic data set containing the details written from the original Logic App.
The Alert Handler Logic App uses an Azure Function to parse the generic data set into a “strongly typed” JSON message that can be parsed, and the values used to create an HTML formatted email.
Steps To Set Up
The following artifacts need to be set up to support business notifications:
- Log Analytics Workspace
- Azure Monitor Common Alert Schema message parse Function
- Alert Handler Logic App
- Azure Alert to monitor for new log messages
- Send Data action in business Logic App
You must create at least one workspace to use Azure Monitor Logs.
- Search for Log Analytics workspaces in Azure Portal
- Click +New and enter subscription, resource group, workspace name, and region
- Select a pricing tier (learn more…). Pay-As-You-Go is sufficient for low volume logs, e.g., business exceptions
- Enter Tags if needed, Review, then create. Workspace creation may be templated
“The common alert schema standardizes the consumption experience for alert notifications in Azure. Historically, the three alert types in Azure today (metric, log, and activity log) have had their own email templates, webhook schemas, etc. With the common alert schema, you can now receive alert notifications with a consistent schema.” (Microsoft Docs link)
The area of interest in the common alert message is alertContext SearchResults. The SearchResults section contains a table of alert details that is split into a list of column names and then an array of related rows, each of which is an array of strings:
Common Alert Message alertContext SearchResults
...snip...
{
"name": "PrimaryResult",
"columns": [
{
"name": "TenantId",
"type": "string"
},
{
"name": "SourceSystem",
"type": "string"
},
{
"name": "MG",
"type": "string"
},
{
"name": "ManagementGroupName",
"type": "string"
},
{
"name": "TimeGenerated",
"type": "datetime"
},
{
"name": "Computer",
"type": "string"
},
{
"name": "RawData",
"type": "string"
},
{
"name": "Source_s",
"type": "string"
},
{
"name": "ID_s",
"type": "string"
},
{
"name": "Message",
"type": "string"
},
{
"name": "Type",
"type": "string"
},
{
"name": "_ResourceId",
"type": "string"
}
],
"rows": [
[
"20956a01-1116-4d05-8dab-c732c5d4c4fe",
"RestAPI",
"",
"",
"2021-05-26T13:00:25.71Z",
"",
"",
"Purchase Order Process",
"100001",
"A business validation error was captured. Details: 'Xxxxxxxx xxxxxxxxxxx'",
"BusinessAlerts_CL",
""
],
[
"20956a01-1116-4d05-8dab-c732c5d4c4fe",
"RestAPI",
"",
"",
"2021-05-26T13:00:25.71Z",
"",
"",
"Purchase Order Process",
"100002",
"A second business validation error was captured. Details: 'Yyyyyyyyy yyy'",
"BusinessAlerts_CL",
""
]
]
}
...snip...
You can see the arrays are not conducive to parsing in a Logic App Parse JSON Data Operation. An Azure Function is used to create a “strongly typed” array:
“Strongly Typed” JSON
[
{
"TenantId": "20956a01-1116-4d05-8dab-c732c5d4c4fe",
"SourceSystem": "RestAPI",
"MG": "",
"ManagementGroupName": "",
"TimeGenerated": "2021-05-26T13:00:25.71Z",
"Computer": "",
"RawData": "",
"Source_s": "Purchase Order Process",
"ID_s": "100001",
"Message": "A business validation error was captured. Details: 'Xxxxxxxx xxxxxxxxxxx'",
"Type": "BusinessAlerts_CL",
"_ResourceId": ""
},
{
"TenantId": "20956a01-1116-4d05-8dab-c732c5d4c4fe",
"SourceSystem": "RestAPI",
"MG": "",
"ManagementGroupName": "",
"TimeGenerated": "2021-05-26T13:00:25.71Z",
"Computer": "",
"RawData": "",
"Source_s": "Purchase Order Process",
"ID_s": "100002",
"Message": "A second business validation error was captured. Details: 'Yyyyyyyyy yyy'",
"Type": "BusinessAlerts_CL",
"_ResourceId": ""
}]
Create a function with the following code to parse the common schema message and produce the “strongly typed” JSON message.
Azure Monitor Common Alert Schema Parser Function
using System;
using System.Collections.Generic;
using System.Dynamic;
using System.IO;
using System.Linq;
using System.Net.Http;
using System.Text;
using System.Threading.Tasks;
using Microsoft.AspNetCore.Http;
using Microsoft.Azure.WebJobs;
using Microsoft.Azure.WebJobs.Extensions.Http;
using Microsoft.Extensions.Logging;
using Newtonsoft.Json;
using Newtonsoft.Json.Converters;
namespace commonFunctions.Schema
{
/// <summary>
/// Azure Monitor Common Alert Schema functions
/// </summary>
public static class AzureMonitorCommonAlertSchemaParser
{
/// <summary>
/// Parse rows in an Azure Monitor Common Alert Schema message and create a well-formed JSON result.
///
/// The common alert schema supplies a list of column names separately to the rows.
/// The rows are merely arrays of values (an array of arrays in reality).
/// This function creates a strongly typed JSON structure.
///
/// Example:
/// ...
/// "columns": [
/// {
/// "name": "FirstName",
/// "type": "string"
/// },
/// {
/// "name": "LastName",
/// "type": "string"
/// }
/// ],
/// "rows": [
/// [
/// "Eric",
/// "Clapton"
/// ],
/// [
/// "Paul",
/// "McCartney"
/// ]
/// ]
/// ...
///
/// Becomes:
/// [
/// {
/// "FirstName": "Eric",
/// "LastName": "Clapton"
/// },
/// {
/// "FirstName": "Paul",
/// "LastName": "McCartney"
/// }
/// ]
///
/// </summary>
/// <param name="request"></param>
/// <param name="log"></param>
/// <returns></returns>
[FunctionName("AzureMonitorCommonAlertSchemaParser")]
public static async Task<HttpResponseMessage> Run([HttpTrigger(AuthorizationLevel.Anonymous, "post", Route = null)] HttpRequest request, ILogger log)
{
log.LogInformation("C# function AzureMonitorCommonAlertSchemaParser started processing a request.");
try
{
var stronglyTypedJsonList = new List<Dictionary<string, object>>();
using (var streamReader = new StreamReader(request.Body))
{
// Read the common alert schema body and convert to a dynamic Expando object in order to find the JSON elements.
var commonAlert = await streamReader.ReadToEndAsync();
dynamic commonAlertBody = JsonConvert.DeserializeObject<ExpandoObject>(commonAlert, new ExpandoObjectConverter());
if (commonAlertBody != null)
{
// Get the PrimaryResult table
var tables = commonAlertBody.data.alertContext.SearchResults.tables;
var primaryResultTable = ((IEnumerable<dynamic>)tables).SingleOrDefault(t => t.name == "PrimaryResult");
if (primaryResultTable == null)
{
throw new KeyNotFoundException("PrimaryResult table not found in common alert schema message");
}
// Get the list of column names. This is converted from a dynamic list to a list
// of objects in order to address by index
var columns =
(from c in ((List<Object>)primaryResultTable.columns).Cast<ExpandoObject>()
select c.First(v => v.Key == "name").Value.ToString())
.ToList();
// Get list of individual data rows (i.e. object list)
var rows =
from row in ((List<Object>)primaryResultTable.rows).OfType<List<Object>>()
select row;
// Iterate the data rows and output with the respective column names e.g. "FirstName": "Paul"
foreach (var row in rows)
{
var keyValuePair = new Dictionary<string, object>();
for (int i = 0; i < columns.Count; i++)
{
keyValuePair.Add(columns[i] ?? string.Empty, row[i]);
}
stronglyTypedJsonList.Add(keyValuePair);
}
}
}
// ========
// Response
// ========
// Return response to caller
var httpResponseMessage = new HttpResponseMessage
{
Content = new StringContent(JsonConvert.SerializeObject(stronglyTypedJsonList), Encoding.UTF8, "application/json")
};
return httpResponseMessage;
}
catch (Exception ex)
{
log.LogError("Error:{0}", ex);
throw;
}
}
}
}
Alert Handler Logic App
The Alert Handler Logic App receives Azure Monitor Common Alert Schema messages from an Azure Alert. This Logic App can do pretty much anything you want with an alert but in this example an HTML formatted email is sent to a selected business user email address.
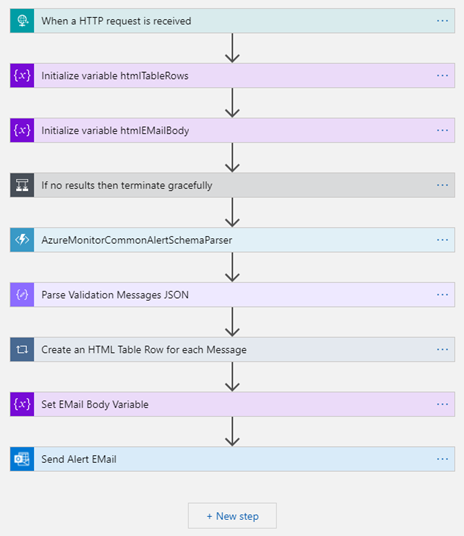
If no results then terminate gracefully
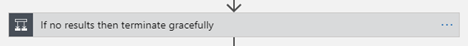
If ResultCount is zero, then no alerts are contained in the message – terminate with Succeeded
@triggerBody()?[‘data’]?[‘alertContext’]?[‘ResultCount’] is greater than 0
Parse Validation Messages JSON
Create a schema that matches the “strongly typed” alert message that is emitted by the parser function.
“Strongly Typed” Schema Example
{
"items": {
"properties": {
"Computer": {
"type": "string"
},
"MG": {
"type": "string"
},
"ManagementGroupName": {
"type": "string"
},
"Message": {
"type": "string"
},
"RawData": {
"type": "string"
},
"SourceSystem": {
"type": "string"
},
"Source_s": {
"type": "string"
},
"TenantId": {
"type": "string"
},
"TimeGenerated": {
"type": "string"
},
"Type": {
"type": "string"
},
"ID_s": {
"type": "string"
},
"_ResourceId": {
"type": "string"
}
},
"required": [
"TenantId",
"SourceSystem",
"MG",
"ManagementGroupName",
"TimeGenerated",
"Computer",
"RawData",
"Source_s",
"ID_s",
"Message",
"Type",
"_ResourceId"
],
"type": "object"
},
"type": "array"
}
Create an HTML Table Row for each Message

Multiple alert rows can be formatted into a table for presentation in the email body.
<tr>
<td class="notification-table-header">
<span> @{items('Create_an_HTML_Table_Row_for_each_Message')?['Source_s']}</span>
</td>
<td class="notification-table-text">@{items('Create_an_HTML_Table_Row_for_each_Message')?['Message']}</td>
</tr>
Set EMail Body Variable

Compose the HTML email body with the table rows created above. The HTML email body should use styles for a professional appearance.
Send Alert Email

Set the email body to the HTML variable, set a subject, and send to a configured email address.
Azure Alert to monitor for new log messages
Search for Alerts in the Azure Portal.

Click + New alert rule

Select the Log Analytics workspace created earlier as the Scope resource.

Create a Condition with an optional where clause

Set Alert logic to be Number of results Greater than 0 threshold value.

Evaluate the alert on a Period of 5 minutes with a Frequency of 5 minutes
Add an Action with an Action Type of Logic App and select the Alert Handler Logic App created earlier.
Set Alert rule details e.g., Severity
Send Data action in Business Logic App
All that is required in the Business Logic App is to send a simple JSON body to Log Analytics using the Send Data action.